Let’s see how you can be tracked while using a VPN and best practices to enhance anonymity.
Ryan Lin, a Massachusetts resident never would have thought the FBI would knock on his door one day. He was caught cyberstalking and torturing his former roommate Jennifer Smith using a ‘no-logs’ PureVPN, which cooperated with the FBI.
While Ms. Smith will be relieved to see the justice served to the criminal (and we all are), this slapped the biggest question to all VPN users:
Can VPNs be Tracked?
Yes, in way more ways than anyone can tell you!
There are mechanisms to back-trace online activity to a user. A well-known way is simply a VPN company buckling under government pressure. This is mostly true for a VPN company headquartered in a surveillance-intensive country.
And I’m not talking about just China or Russia. According to various reports, the famous 14 eyes alliance is notorious for sharing intel about each other’s citizenry, circumventing the laws that prohibit them from prying on their own countrymen.
So while you sign up for a VPN, look at their head office. Avoiding these regimes would help keep things private.
However, that’s just the first step, and there are others to ensure a more private experience while using a VPN.
Note: The following sections are valid for good VPNs with a strict no-logs policy and a privacy-respecting track record. The substandard ones often track their own users themselves or allow easy tracking by third parties, making them effectively useless for user privacy.
Active Google Accounts
The first thing I do in a new browser is sign in to my Google accounts. And that’s not just to use Google services, the primary intention is to use the Google sign-in with other websites.
Ergo, if you have an active Google account, using a VPN won’t shield you from tracking. Though the VPN will assign you a different IP address, Google still knows it’s you.
And you get browser-history-related adverts across the internet, confirming the snooping.
However, this isn’t just about Google. Even a ‘running’ social account like Facebook can be privacy-invasive. Because if they have their own ad network, most certainly, they will track your web activity to power their targeted advertisements.
So, sign out of unnecessary logins or use browser incognito mode.
Server Obfuscation
Obfuscated servers mean no one can tell if you’re using a VPN. The network traffic is disguised as regular web activity evading unwanted attention.
This helps the users to avoid giving away usage of the common VPN protocols (OpenVPN, Wireguard, etc.), which anyone can check using data packet analyzers like Wireshark.
In addition, obfuscation is effective in bypassing firewalls like that of China.
However, even most top-level VPNs lack this feature. And frankly, it’s not easy for the average commoner to confirm its perfect implementation.
Still, it’s best to confirm server obfuscation in the VPN features before paying.
Browser Fingerprinting
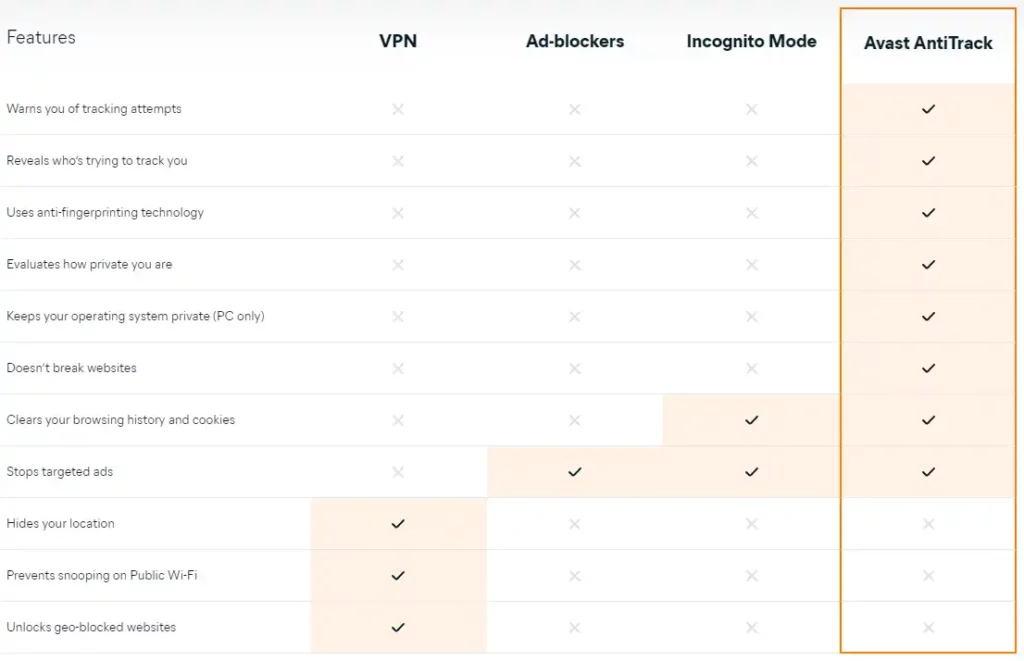
Browser or Digital Fingerprinting is user profiling based on their browser type, operating system, timezone, and a ton of other information.
The primary use of fingerprinting is targeted advertisement. And oftentimes, using the native browser protections isn’t enough to protect you.
In fact, VPNs aren’t the choice of weapon for this as they can’t help much in anti-tracking, the primary domain covering fingerprinting.
The best bet here would be subscribing to Ghostery. This is anti-track, adblocker, tracker analysis, private search, etc., rolled in one. Besides, Ghostery is 100% open-source which adds to its legitimacy.
However, this is a paid option, and not all of us want to pay for anti-tracking.
So, the second best option is using the free Privacy Badger while using a VPN to avoid tracking. In addition, you can switch to Firefox or Brave to get maximum benefit.
Single Hop
Correlation attacks are extremely sophisticated and rare mechanisms to match entry and exit traffic irrespective of the encryption. In short, in a closed world setting and with substantial computing power, it’s possible to tell which websites a user visits using timing and data transfer.
Interested in Correlation attacks? Check this research paper about website fingerprinting targeting encrypted channels.
However, its real-life implementation is a distant dream. Besides, the sheer amount of resources needed to perform such a correlation attack makes it worthless to victimize a standard user.
Ergo, rest assured, you’re safe if you aren’t a person of interest, comparable to the Edward Snowdens of the real world.
Still, you can search for Multi-hop where the data goes through two VPN servers. Additionally, Tor over VPN is another excellent feature to ask for if you expect top-level privacy.
Final Words
So, can VPNs be tracked? Yes!
But 100% privacy is often not important for regular VPN users, and a huge chunk of people use a VPN for entertainment.
Still, if you are subscribed to a robust VPN while ensuring the above-mentioned best practices, there is little to worry about. Besides, go through their privacy policy to see what data they collect and if you’re okay with it.
And if you’re wondering, I would recommend ProtonVPN (also has a free tier), Surfshark, and Mullvad VPN.
PS: If privacy is the crucial factor, you should consider switching to DuckDuckGo. This will keep you (almost) free from the ‘regular’ tracking. Check if using DuckDuckGo is safe and how it makes money if not targeted advertisement.